Chapter 8: How SSH Password Authentication Works
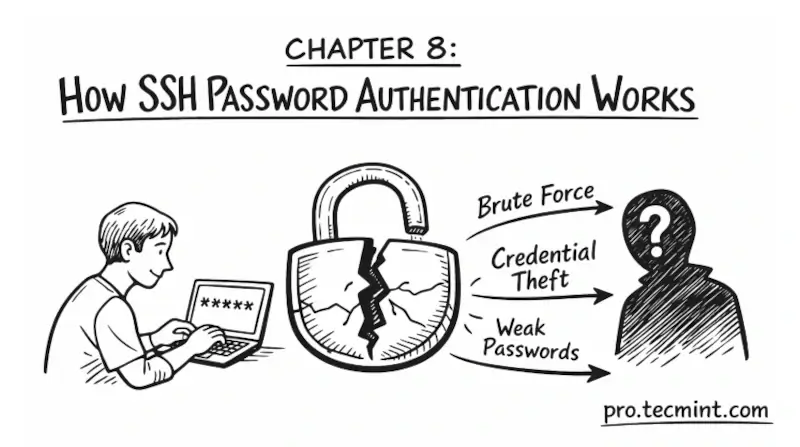
In Chapter 8, you'll learn how password authentication works under the hood, why it's a serious security risk for any public-facing server, and the safe sequence to follow before disabling it entirely.
In the previous chapter, you learned how to troubleshoot the most common SSH connection errors.
By now, you have successfully connected to a remote server using SSH and have a solid understanding of what happens at each step of the connection process.
In this chapter, you will take a closer look at the first and most familiar authentication method called password authentication.
You will learn exactly how it works under the hood, why it is considered risky, and why professional sysadmins and DevOps engineers move away from it as quickly as possible.