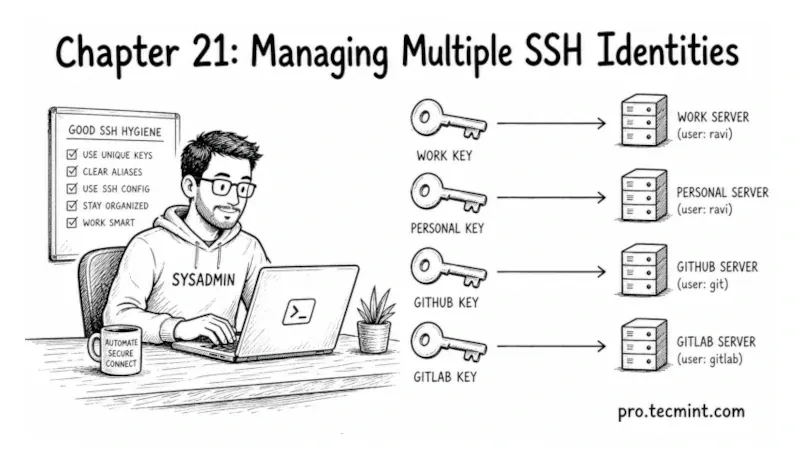
Chapter 21: Managing Multiple SSH Identities
In this chapter, you'll learn how to manage multiple SSH identities, assign keys per host, and use IdentitiesOnly to eliminate authentication failures.
In the previous chapter, you learned what the SSH agent is, how to start it, add keys to it, and keep it running cleanly across terminal sessions.
You now have a workflow where you unlock your key once per session, and SSH handles authentication silently from that point on.
But most sysadmins and DevOps engineers do not have one server and one key. They have work servers, personal servers, GitHub, GitLab, a home lab, and a client's infrastructure - each with different keys, different usernames, and different connection requirements.
Without a proper system for managing this, SSH either uses the wrong key, tries too many keys and hits the server's authentication limit, or falls back to prompting you every time.
In this chapter, you will build that system using ~/.ssh/config and the SSH agent together to ensure SSH always uses the right key for the right destination, automatically.