Chapter 9: Introduction to Public Key Cryptography
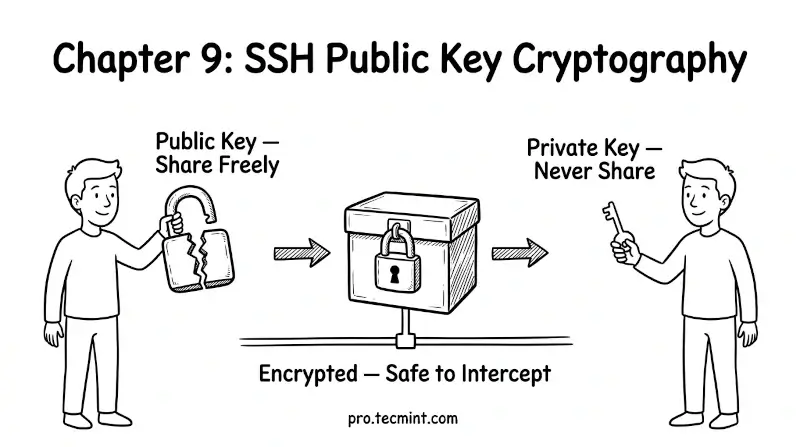
In Chapter 9, you'll learn what public key cryptography actually is, how the two-key system works, and why your private key never needs to leave your machine to prove your identity to a server.
In the previous chapter, you learned how password authentication works and why it is a security liability for any server exposed to the internet. You saw that passwords can be brute-forced, stolen, and do not work well in automated workflows.
The solution to all of these problems is public key cryptography - the foundation that SSH key-based authentication is built on.
Before you generate your first SSH key pair in the next chapter, you need to understand the concept behind it. Once you do, everything about SSH keys will make complete sense.

