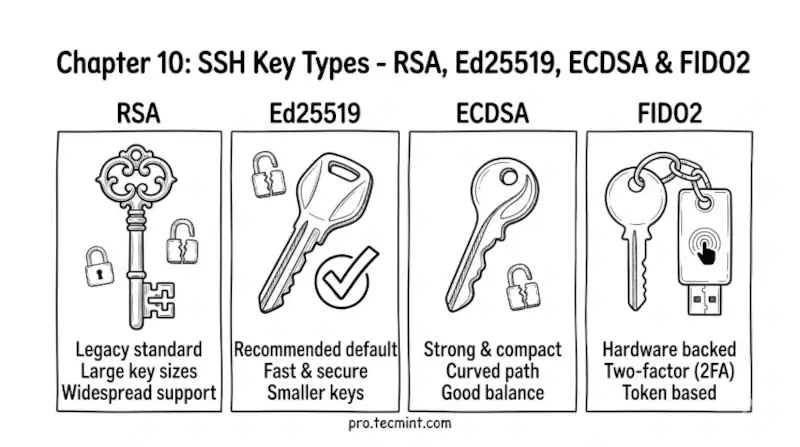
Chapter 10: SSH Key Types - RSA, Ed25519, ECDSA & FIDO2
In Chapter 10, you will learn about the different types of SSH keys available, including RSA, Ed25519, ECDSA, and FIDO2 hardware keys.
In the previous chapter, you learned how public key cryptography works and why SSH key-based authentication is fundamentally more secure than passwords.
You now understand that you need a key pair - a private key that stays on your machine and a public key that goes on the server.
Before you run ssh-keygen and generate your first key pair, you need to make one decision - which key type to use.
SSH supports several different key types, each based on different cryptographic algorithms, and choosing the right one before you generate anything will save you from having to redo it later.
In this chapter, you will learn what each key type is, how they compare, and which one you should use.