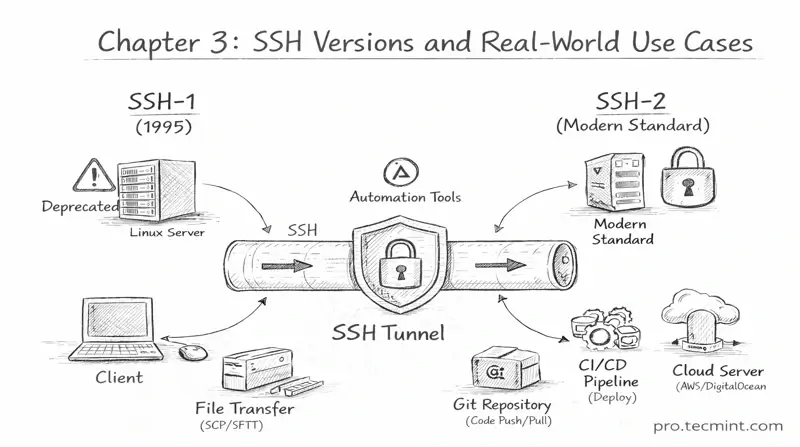
Chapter 3: Understanding SSH-1, SSH-2, and Use Cases
Learn how SSH-1 and SSH-2 differ and how SSH is used for remote administration, file transfers, and CI/CD pipelines.
In the previous chapter, you learned how SSH establishes a secure connection between a client and a server through a seven-step handshake.
Now that you understand how SSH works internally, the next step is to learn about the two versions of the SSH protocol and how they differ.
SSH-1 vs SSH-2
When working with SSH, you may have seen the terms SSH-1 and SSH-2.
These refer to two different versions of the Secure Shell protocol, and understanding the difference between them is important.
Because one version is obsolete and insecure, while the other is the modern standard used in production systems today.
SSH-1 - The Original
SSH-1 was created in 1995 by Finnish researcher Tatu Ylönen, and at that time, it was a major improvement over existing remote access tools.
Before SSH, administrators commonly used protocols such as Telnet to log in to remote machines, but the problem with Telnet was that it transmitted data in plain text, which meant that usernames, passwords, and commands could be easily intercepted by anyone monitoring the network.
SSH-1 solved this problem by introducing encryption for remote sessions between the client and server, so that data traveling on the network could no longer be read by attackers listening on the network, which made remote administration significantly more secure.
Because of this improvement, SSH-1 was rapidly adopted across Unix and Linux systems and became the standard method for secure remote login.
However, as SSH-1 became widely used, security researchers started to find serious weaknesses in its design.
The biggest problem was that it relied on older encryption algorithms, such as DES and 3DES, which were later found to have security vulnerabilities.
It also had problems with how it verified the integrity of data, which meant an attacker could potentially inject malicious data into an active SSH session.
These were not minor problems but basic design flaws in the protocol, and because of these weaknesses, SSH-1 could not simply be fixed with small updates or patches, so the only real solution was to redesign the protocol completely and build a new version from scratch.